This is a student-safe environment to learn and tinker with SQL queries without […]
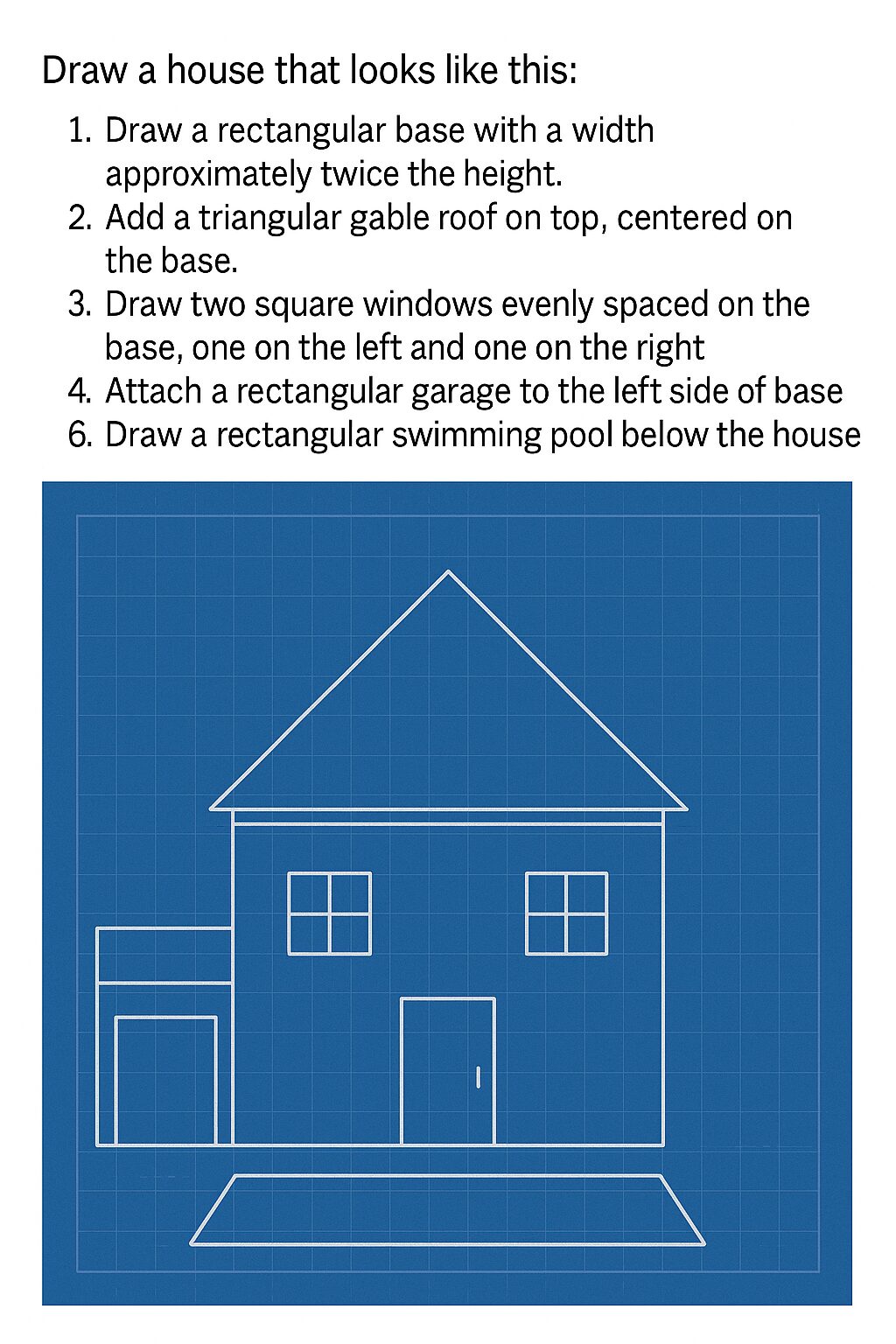
Teaching the Bubble Sort Algorithm using Pringles Creative Commons Simon Rundell CC NC-BY-SA […]
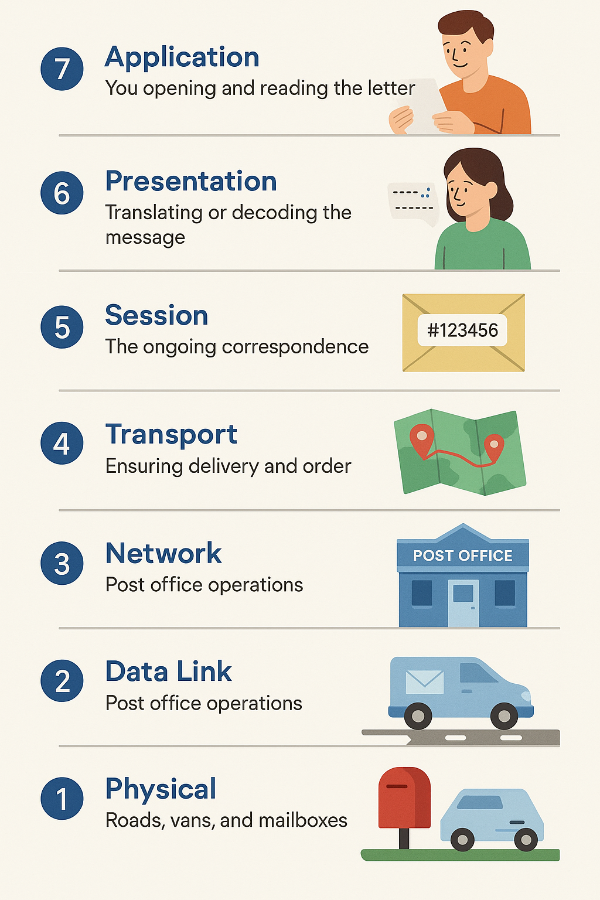
A network layer model helps break down communication into smaller, more manageable functions. […]
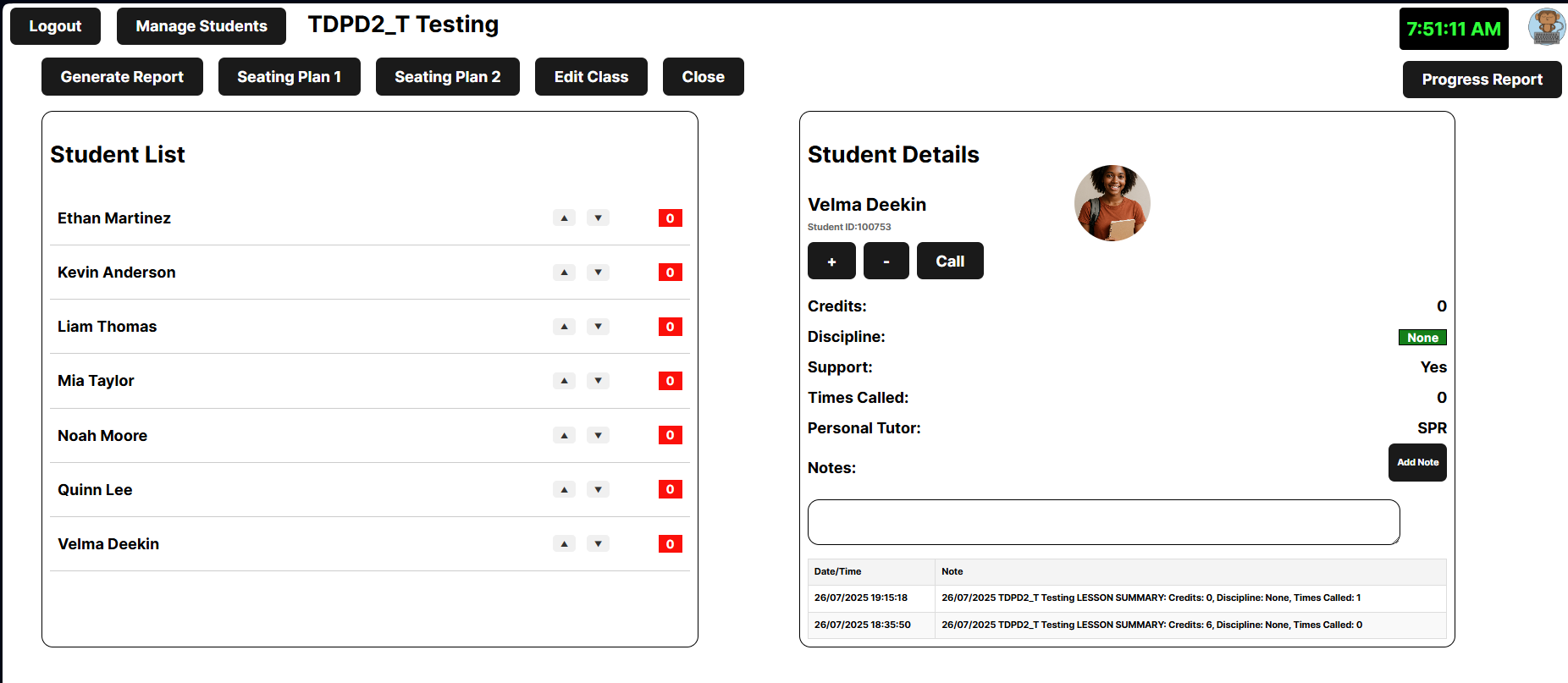
Tablet-based tracker for in-Classroom use. Tracking pupils mid lesson is hard. I am […]
This is the lesson plan which got me the job. I couldn’t be […]
Many schools often ban Mobile Phones as a distraction, but in Computing we […]